In AHP the preference Pi of alternative Ai is usually calculated using the weigthed sum model (WSM), i.e. calculation of global priorities for alternatives results from the additive aggregation of local preferences and criteria weights.
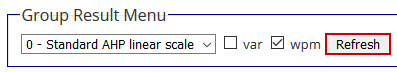
In my online software AHP-OS users can also select the weighted product model (WPM), where alternatives are aggregated using the product instead of the sum (Goepel 2018). We call this – in contrast to the classical (additive) AHP – multiplicative AHP or MAHP.
Ishizaka, Balkenborg and Kaplan (2011) have shown that the additive AHP will overrate alternatives with extreme ratings and penalize balanced ones. Bafahm and Sun (2019) examine in their paper some abnormal results of AHP, contradictory to common expectations and basis decision-making logic in very simple cases. These conflicting results can be easily avoided using WPM.
Krejci and Stoklasa (2018) clearly show in their paper the superiority of using the weighted product model over the weighted sum model for the purpose of deriving global priorities of alternatives.
Aggregation of local priorities of alternatives into global priorities in AHP should not be done using the weighted sum model (WSM). Instead, the Weighted Product Method (WSM) should be used.
Literature
Bafahm A., Sun M. (2019). Some Conflicting Results in the Analytic Hierarchy Process, International Journal of Information Technology & Decision Making Volume 18, Issue 02 (March 2019) Pages:419–443 https://doi.org/10.1142/S0219622018500517
Goepel, K.D. (2018). Implementation of an Online Software Tool for the Analytic Hierarchy Process (AHP-OS). International Journal of the Analytic Hierarchy Process, Vol. 10 Issue 3 2018, pp 469-487 https://doi.org/10.13033/ijahp.v10i3.590
Ishizaka A., Balkenborg D., Kaplan T. (2011). Influence of aggregation and measurement scale on ranking a compromise alternative in AHP. Journal of the Operational Research Society (2011) 62: 700. https://doi.org/10.1057/jors.2010.23
Krejci J., Stoklasa J. (2018). Aggregation in the analytic hierarchy process: Why weighted geometric mean should be used instead of weighted arithmetic mean. Expert Systems with Applications Volume 114, 30 December 2018, Pages 97-106 https://doi.org/10.1016/j.eswa.2018.06.060
 Operating your own website or blog, you will soon realize lots of comments with nonsense content and embedded links to obscure websites. These are comment spammers making your life difficult. Everyday you have to clean up or moderate all comments. In the past I used a wordpress plugin “spam free wordpress” to protect my blog, and for long time it was working fine without any problems. Writing a comment to my postings, you were asked to copy and paste a password from one to another field in the comment form. Suddenly it was not working any longer, and I found out that the developer changed his policy: I have to pay a license fee.
Operating your own website or blog, you will soon realize lots of comments with nonsense content and embedded links to obscure websites. These are comment spammers making your life difficult. Everyday you have to clean up or moderate all comments. In the past I used a wordpress plugin “spam free wordpress” to protect my blog, and for long time it was working fine without any problems. Writing a comment to my postings, you were asked to copy and paste a password from one to another field in the comment form. Suddenly it was not working any longer, and I found out that the developer changed his policy: I have to pay a license fee. 






